For decades, intrusion detection systems (IDS) relied on a simple but effective philosophy: identify known threats by matching network traffic against a database of attack signatures. This approach, while reliable against established exploits, left networks vulnerable to novel or highly adaptive attacks. Today, a paradigm shift is underway, driven by machine learning (ML), autonomous agents, and tools like SnortML. Instead of asking "does this match a known pattern?" modern systems are beginning to ask a far more powerful question: "does this actually make sense in context?"
The Limitations of Signature-Based Detection
Signature-based detection is essentially a game of pattern matching. Each known threat—be it a worm, a buffer overflow, or a SQL injection—is reduced to a unique fingerprint. When a packet or sequence of packets matches that fingerprint, an alarm sounds. This method is fast, low on false positives, and easy to deploy. However, it suffers from three critical shortcomings:
- Zero-day vulnerability: Novel attacks that have never been seen before cannot be detected because no signature exists.
- Polymorphic and metamorphic malware: Malware that changes its code or behavior while preserving its malicious intent can easily evade signature checks.
- High maintenance overhead: Security teams must constantly update signature databases, a labor-intensive process that can lag behind emerging threats.
As attackers become more sophisticated, the need for a detection paradigm that goes beyond static rules becomes urgent.
Enter Machine Learning and SnortML
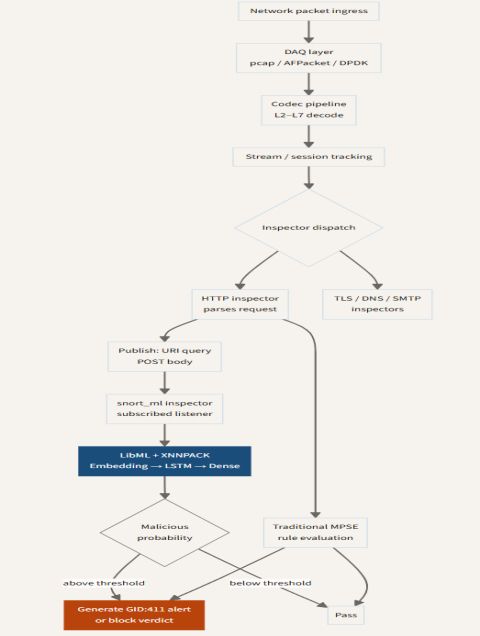
Machine learning offers a way out of the pattern-matching dead end. Instead of relying on predefined fingerprints, ML models learn the normal behavior of network traffic and then flag deviations as suspicious. SnortML, an extension of the popular Snort IDS, integrates such models directly into the detection pipeline. It can analyze flow data, payload characteristics, and protocol anomalies to identify threats that no signature could catch.
For example, an ML model might learn that a certain server typically receives around 100 connection requests per minute. If that volume suddenly spikes to 10,000, the system can alert on the anomaly—even if the individual packets are not malicious per se. This approach shifts the focus from what the attack looks like to what the attack does in the context of the environment.
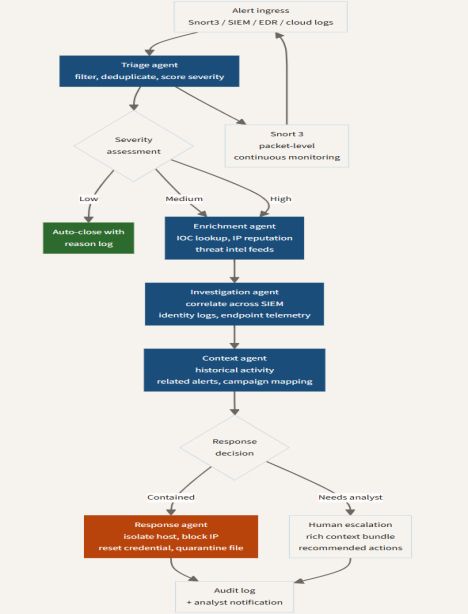
Agentic AI: Autonomous Decision-Making
Moving a step beyond passive ML models, agentic AI introduces autonomous agents that can perceive, reason, and act within the network. These agents are not merely classifiers; they are decision-makers. An agent might correlate alerts from multiple sensors, query threat intelligence feeds in real time, and even initiate a temporary firewall rule to block a suspicious IP—all without human intervention.
This evolution transforms the IDS from a passive monitor into an active participant in network defense. Agentic AI can adapt to changing conditions, learn from past incidents, and coordinate responses across different security layers. The key here is context: the agent not only detects an anomaly but understands its relevance within the broader operational picture.
The Shift to Contextual Analysis
The marriage of machine learning and agentic AI leads to a fundamental change in detection logic. Traditional systems operate on a binary: traffic either matches a signature (malicious) or it does not (benign). Contextual analysis, however, evaluates behavior on a spectrum. A single failed login attempt might be benign, but a thousand attempts from a foreign IP in 30 seconds, targeting a privileged account, is highly suspicious—even if no known hacking tool signature is present.
Context includes factors such as:
- Time of day and historical baselines of network activity
- User identity and role (e.g., an employee accessing a server they never use)
- Protocol violations or unusual combination of services
- Correlation with external threat intelligence feeds
By analyzing these dimensions, a contextual system reduces false positives and catches attacks that would slide past signature-based tools.
Challenges and Future Directions
Despite its promise, the contextual approach is not without challenges. Machine learning models require large, high-quality datasets to train effectively, and they can be vulnerable to adversarial manipulation—attackers feeding carefully crafted inputs to deceive the model. Agentic AI, if not properly constrained, could make autonomous decisions that disrupt legitimate traffic or escalate incidents unnecessarily.
Moreover, deploying such intelligent systems demands higher computational resources and specialized expertise. Many organizations still rely on signature-based IDS as their primary line of defense. The transition to ML and agentic solutions will likely be gradual, with hybrid architectures that combine the best of both worlds.
Conclusion
The era of "does this match a known pattern?" is giving way to the era of "does this actually make sense in context?" With tools like SnortML and the rise of agentic AI, intrusion detection is evolving from a reactive, signature-bound discipline into a proactive, context-aware science. Security teams that embrace this shift will be better equipped to defend against the unknown, adaptive threats of tomorrow. The sensor is indeed starting to think—and that thinking may be our best hope for staying ahead of the adversary.